MAGICO DCSD Cable Engineering iPhone Serial Port Cable Engineering Exploit USB Cable for iPhone 7/7P/8/8P/X - AliExpress

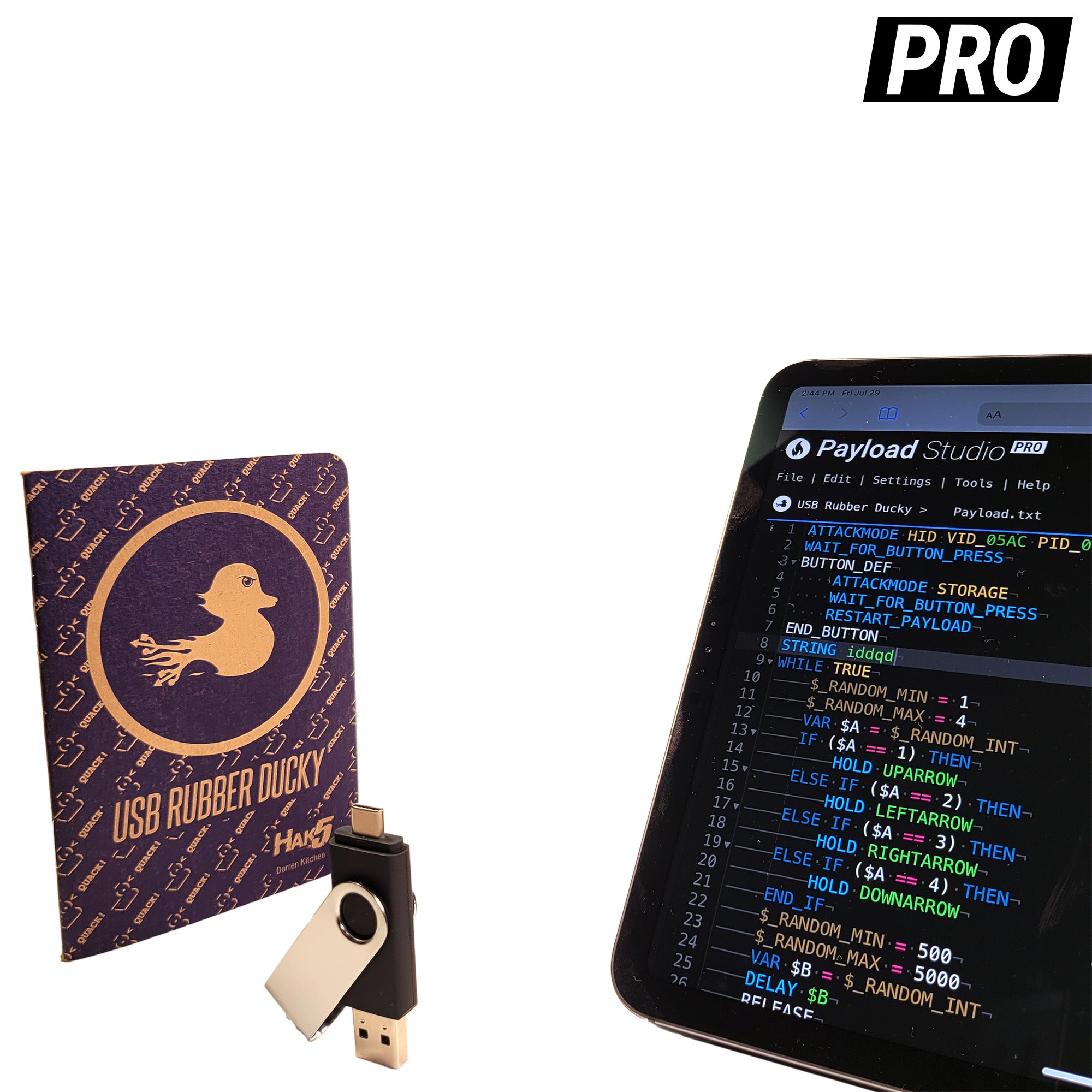
Defending against weaponized hardware: Windows Defender ATP & Microsoft Intune to the rescue! A story about RubberDucky & an evil mouse | by Maarten Goet | Medium





/cdn.vox-cdn.com/uploads/chorus_asset/file/23949203/226141_rubberDucky.jpg)